TL;DR
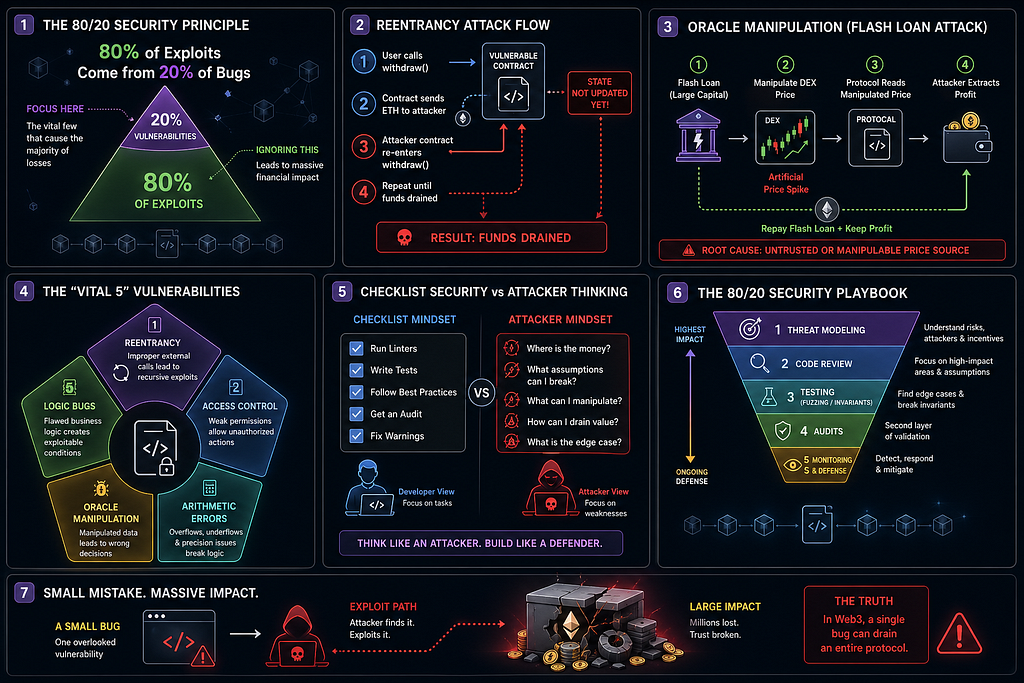
Most smart contract exploits come from a small set of recurring vulnerabilitiesFocus on the “Vital 5”: reentrancy, access control, arithmetic edge cases, oracle manipulation, and logic flawsShift from checklist security → risk based, attacker first thinkingApply an 80/20 security playbook: threat modeling, targeted reviews, fuzzing, and runtime monitoringSecurity isn’t about doing everything it’s about doing the right things extremely well
The Hard Truth About Smart Contract Security
In Web3, exploits aren’t rare edge cases they’re systemic.
Billions of dollars have been lost across DeFi protocols, often due to bugs that were neither novel nor sophisticated. The uncomfortable reality is this:
Most catastrophic exploits are caused by well known, preventable vulnerabilities.
Not zero days. Not cutting edge cryptography failures.
Just mistakes we’ve seen before over and over again.
This creates a paradox:
Security feels complex and overwhelmingBut the majority of risk comes from a small, predictable set of issues
That’s where the 80/20 Principle becomes a powerful lens.
If you focus on the critical few vulnerabilities that cause the majority of losses, you can dramatically improve your security posture without infinite effort.
The 80/20 Principle in Web3 Security
The Pareto Principle states:
80% of outcomes come from 20% of causes
In smart contract security, this translates to:
80% of exploits come from 20% of vulnerability classesA handful of design and implementation mistakes repeatedly lead to catastrophic failures
Why this matters:
Smart contracts are immutable and adversarial by defaultSmall bugs can control large capital poolsAttackers are highly incentivized and operate with asymmetric advantageIn Web3, a single overlooked line of code can invalidate an entire protocol’s security model.
Your goal is not perfect security it’s prioritized security.
The “Vital 5” High Impact Solidity Vulnerabilities
If you master these five categories, you eliminate the majority of real world risk.
1. Reentrancy
What it is:
A contract calls an external contract before updating its own state, allowing the external contract to re-enter and manipulate execution flow.
Why it’s dangerous:
It breaks assumptions about atomic execution.
Classic exploit pattern:
User withdraws fundsContract sends ETH before updating balanceAttacker re-enters withdraw functionDrains funds recursively
Mitigation strategies:
Use Checks Effects Interactions patternApply reentrancy guardsPrefer pull over push paymentsIf your contract sends value before updating state, you’re already in danger.
2. Access Control Flaws
What it is:
Improper permission checks or missing restrictions on sensitive functions.
Common examples:
Anyone can call mint()Admin role not properly enforcedInitialization functions callable multiple times
Why it’s dangerous:
Access control bugs often lead to total protocol compromise.
Mitigation strategies:
Use established patterns (e.g., role based access control)Clearly define:Admin rolesUpgrade permissionsEmergency controlsLock initialization functions after deploymentMost “hacks” are just unauthorized access disguised as complexity.
3. Integer Overflows / Underflows (Post Solidity 0.8 Context)
What it is:
Arithmetic errors that wrap values beyond their limits.
Context:
Solidity ≥0.8 automatically reverts on overflow/underflow but issues still exist:
Unchecked blocks (unchecked {})Precision loss in divisionRounding errors in financial logic
Why it’s dangerous:
Math errors can:
Inflate balancesBreak invariantsEnable economic exploits
Mitigation strategies:
Avoid unnecessary uncheckedUse consistent scaling (e.g., 1e18)Carefully audit all financial formulasIn DeFi, math is not implementation detail it is the protocol.
4. Oracle Manipulation
What it is:
Exploiting weaknesses in price feeds or external data sources.
Common vectors:
Using spot prices from DEXsLow liquidity poolsFlash loan manipulation
Exploit pattern:
Borrow large capital via flash loanManipulate price on-chainTrigger protocol logic (liquidation, minting, etc.)Extract profitRepay loan
Mitigation strategies:
Use timeweighted average prices (TWAP)Prefer trusted oracle networksValidate price deviationsAvoid single source dependencyIf your protocol trusts a price, attackers will try to control it.
5. Logic Bugs in DeFi Protocols
What it is:
Flaws in business logic not syntax or low-level errors.
Examples:
Incorrect reward calculationsBroken collateralization checksInconsistent state transitions
Why it’s dangerous:
These are:
Harder to detectOften pass auditsHighly exploitable
Mitigation strategies:
Define clear invariantsSimulate adversarial scenariosReview logic like an attacker, not a developerMost expensive bugs aren’t technical they’re conceptual.
The Security Mindset Shift
Most teams approach security like a checklist:
Run a linterAdd SafeMathWrite unit testsGet an audit
But attackers don’t think in checklists.
They think in attack surfaces, incentives, and edge cases.
Why teams over focus on low impact issues:
Static analysis tools highlight minor issuesAudits produce long reports with mixed severityDevelopers optimize for “clean code,” not adversarial resilience
What actually matters:
Security is about reducing exploitability, not eliminating warnings.
Shift your thinking:
From: “Did we follow best practices?”To: “How would I break this system if millions were at stake?”
The 80/20 Security Playbook
Here’s a practical framework to apply immediately.
1. Threat Modeling (Start Here)
Ask:
What assets are at risk?Who are the attackers?What are the economic incentives?What assumptions does the system rely on?
Focus on:
Fund flowsExternal dependenciesPrivileged roles
Output: A list of high risk attack scenarios
2. Code Review Priorities
Don’t review everything equally.
Focus heavily on:
State transitionsExternal callsAccess modifiersFinancial calculations
Ask:
Can this function be abused?What happens in edge cases?What assumptions are implicit?
3. Testing Strategy (High ROI Only)
Skip shallow coverage. Focus on depth.
Must have layers:
Unit tests
Cover core logic paths
Fuzz testing
Randomized inputs to uncover edge cases
Invariant testing
Define truths that must always hold
(e.g., total supply consistency)If you’re not testing invariants, you’re not testing DeFi.
4. Audits vs Internal Security
Audits are valuable but not a silver bullet.
Reality:
Auditors have limited timeThey don’t fully understand your intentThey can miss logic flaws
Best approach:
Do strong internal reviews firstUse audits as second layer validationTreat findings as starting points, not conclusions
5. Post Deployment Defenses
Security doesn’t end at deployment.
Add:
Monitoring systems (track anomalies)Circuit breakers / pause mechanismsUpgrade paths (if applicable)Bug bounty programsThe fastest way to lose funds is assuming your job is done after deployment.
Case Study 1: Reentrancy The Classic That Keeps Winning
A protocol allows withdrawals via:
Send ETH to userUpdate user balance
An attacker:
Deploys a malicious contractCalls withdrawRe-enters before balance updateDrains funds
Why it happened:
Violated Checks Effects InteractionsNo reentrancy guard
Lesson:
Known vulnerabilities are still the most dangerous because they’re ignored.
Case Study 2: Oracle Manipulation in DeFi
A lending protocol uses a DEX spot price as collateral value.
Attacker:
Takes flash loanManipulates DEX priceBorrows against inflated collateralExtracts fundsRepays loan
Why it happened:
Trusted manipulable price sourceNo TWAP or validation
Lesson:
Any external dependency is a potential attack vector especially price feeds.
Final Takeaway
Smart contract security isn’t about doing more.
It’s about doing what matters.
If you eliminate the “Vital 5” vulnerabilities, you eliminate most real-world risk.
The teams that get hacked aren’t always careless they’re often just misprioritized.
Focus on:
High impact vulnerabilitiesAttacker mindsetRisk driven engineering
And remember:
In Web3, you don’t get hacked because you missed everything. You get hacked because you missed the one thing that mattered.
Quick 80/20 Security Checklist
Did we model real attack scenarios?Are external calls safe from reentrancy?Is access control airtight?Are financial calculations precise and consistent?Are price feeds manipulation-resistant?Do invariants hold under fuzz testing?Do we have monitoring and emergency controls?
Security is leverage.
Focus on the 20% that protects the 80%.
The 80/20 Principle in Smart Contract Security: How to Prevent 80% of Exploits with 20% Effort was originally published in Coinmonks on Medium, where people are continuing the conversation by highlighting and responding to this story.