At QuillAudits, after 1,500+ audits over eight years, here’s the truth nobody wants to hear:
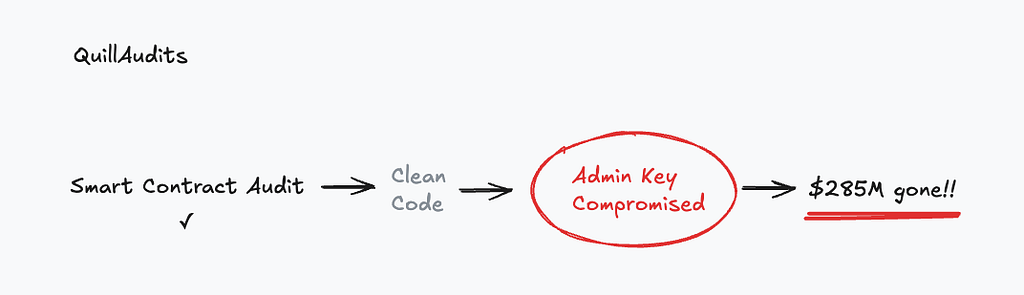
Your smart contract audit covers roughly 30% of your actual attack surface.
The other 70% is what drained Drift, Radiant, Resolv, WazirX, and Bybit for over $2 billion combined. None were code bugs. Every single protocol had passed a smart contract audit.
The Pattern Is Clear
April 2026. Drift Protocol. $550M TVL. Audited by a top-tier firm. Gone in twelve minutes.
The contracts were flawless. Attackers spent six months socially engineering the team, exploited Solana’s durable nonce feature, and drained half the TVL before anyone could react.
Before that: Radiant lost $50M through malware that displayed legitimate transactions while malicious ones were signed in the background. Bybit lost $1.4B the largest crypto theft in history, through a compromised laptop that manipulated what signers saw on screen.
We audit the vault door. Attackers walk in through a window nobody was watching.
What an Admin Audit Actually Covers
A smart contract audit reviews your Solidity. An Admin Audit reviews everything else, keys, multisigs, cloud infrastructure, signer devices, social engineering resistance, timelocks, and incident response.
Here are the four most critical questions every founder must answer tonight:
1. Can you list every privileged key in under 5 minutes? Admin keys, multisigs, service accounts, cloud IAM roles, deployment keys. If you can’t, that’s your first finding. Resolv’s single-EOA minting key was never flagged because nobody asked.
2. If one signer is compromised tomorrow, what can they do? If the answer is something critical, your threshold is wrong. Make that number high. Distribute signers geographically. Include at least one external signer outside your organization.
3. Do your signers verify what they sign, or just trust the UI? This is where Radiant and Bybit died. Always simulate transactions on independent tools. Decode and verify raw calldata outside the wallet UI. Never sign blindly.
4. If an attacker gains admin access right now, how fast can they drain everything? If the answer is “immediately,” you have a design flaw no smart contract audit will ever catch. Timelocks on all critical actions 24 — 48 hours minimum are the cheapest insurance policy in DeFi.
The Bottom Line
$3 billion+ in losses didn’t come from buggy code. They came from governance decisions founders either made poorly or didn’t make at all.
Multisig thresholds too low. Timelocks that didn’t exist. Signing keys sitting in cloud environments, nobody audited.
The code was fine. The keys were not.
Smart Contract Audit + Admin Audit = Complete Protocol Security.
Want to go deeper? We’ve covered all 7 critical questions, real exploit breakdowns, and the full Admin Audit framework in our detailed blog on Admin Audit & Web3 OPSEC Security.
The Admin Audit Checklist was originally published in Coinmonks on Medium, where people are continuing the conversation by highlighting and responding to this story.